May 14 2026
Opening Ceremony
Welcome to NorthSec 2026!
Hacking Dumberly
-
Tim Medin
Private Key Leaks in the Wild: Insights from Certificate Transparency
-
Guillaume Valadon GitGuardian
-
Gaetan GitGuardian
A systematic approach to evading antivirus software
-
Philippe Pépos Petitclerc Université du Québec à Montréal
Doxxing-proof authentic digital media: trust the asset, protect the source
-
Christian Paquin Microsoft Research
Sold to the highest bidder : the escalation of ADINT from geolocation tracking to intrusion vector
-
Maxime ARQUILLIERE Sekoia.io
-
Coline C Sekoia.io
Living Off The Pipeline: Defensive Research, Weaponized
-
François Proulx BoostSecurity.io
Hacking 5G: From Radio Security to the APIs
-
Sébastien Dudek Penthertz
Hacking Browsers: The Easy Way
-
Robbe Van Roey Aikido
Stolen Laptops : Defeating DMA Countermeasures
-
Pierre-Nicolas Allard-Coutu Bell Canada
From Experts to Everyone: Democratizing Threat Modeling at Ubisoft
-
Kristine Barbará Ubisoft Entertainment
Increasing detection engineering maturity with detection as code
-
Émilio Gonzalez
Offensive Security and Threat Modeling, an unlikely collaboration
-
Jonathan Marcil
-
Martin Dubé Corsek
Mapping Deception Solutions with BloodHound OpenGraph
-
Joshua Prager SpecterOps Inc.
-
Ben Schroeder
Researchers vs. Threat Actors in Cloud Attacks
-
Dirk-jan Mollema Outsider Security
-
Sanne Maasakkers Mandiant (part of Google Cloud)
The OpenGraph diary: Attack path management applied to Ansible
-
Charl-alexandre Le Brun Desjardins
-
Simon Lachkar Desjardins Group
Podcast PolySécure
Podcast live sur la scène!
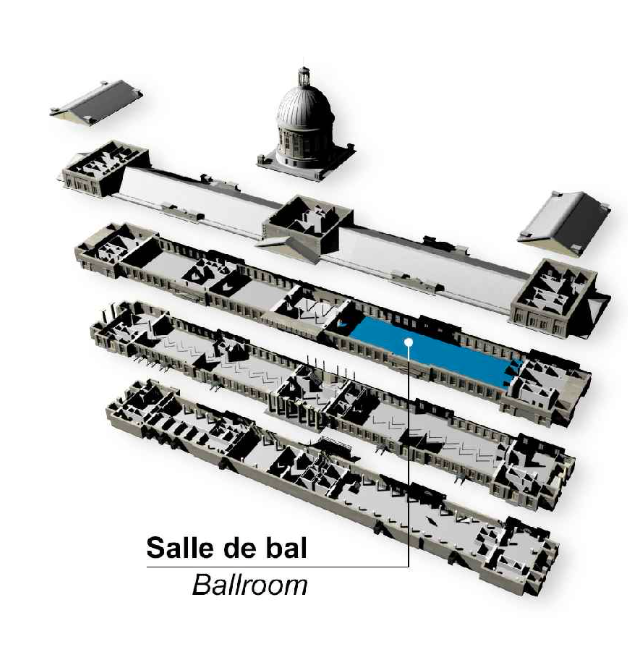
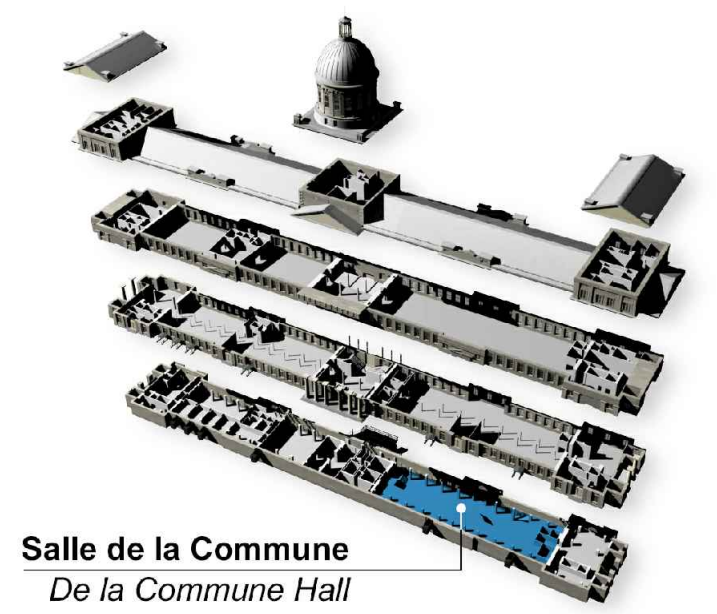
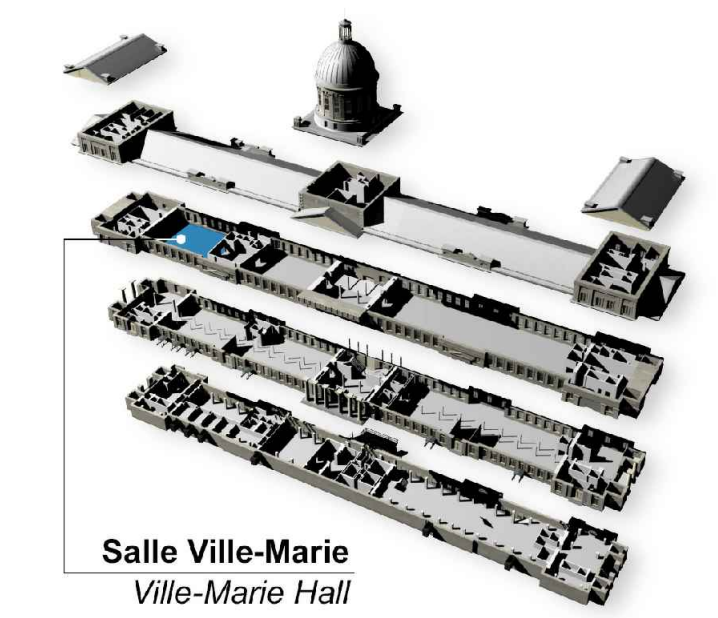
Party du jeudi / Thursday Party
Rejoins-nous pour le party thématique de NorthSec: Party en lumière
Avec :
- Temporal Waves
- Samajam
- DJāy b2b Pocaille
- Cocktails thématiques, incluant des options sans alcool
N'oubliez pas votre tenue Solarpunk/lumineux/blanc.
Les portes ouvrent à 19h
En bonus: Les matchs des Canadiens de Montréal seront diffusés au Marché Bonsecours dès 19h. Billet requis.
//
Join us for the NorthSec themed party: Party in the Light
Featuring:
- Temporal Waves
- Samajam
- DJāy b2b Pocaille
- Themed cocktails, including non-alcoholic options
Don’t forget your solarpunk/glowing/white outfit.
Opens at 7 pm
Bonus: Montreal Canadiens games will be broadcast at Marché Bonsecours starting at 7 p.m. Tickets required.
May 15 2026
Lost in the AI Woods: Why the Future Still Needs You -- A Dual Keynote
-
Varsha Dwarakanathan Bloomberg
-
Salini Mishra Bloomberg
Commit, Push, Compromise: Attacking Modern GitHub Orgs
-
Andrew Buchanan Figment
-
Max CM Figment
Internet Blackout 2026 in Iran — Next-Level Internet Censorship: A Technical Breakdown of Techniques and Tactics.
-
Reza Sharifi CGI Deutschland
Trust me, I'm a Shortcut - new LNK abuse methods
-
Wietze
Cybermenaces géopolitiques au Canada : État des lieux et perspectives stratégiques
-
Philippe Marchand Chaire Raoul-Dandurand
Red Teaming Mindset and Methodology
-
Charles F. Hamilton (Mr.Un1k0d3r) CYPFER
Le futur s'invente avant-hier
-
Xavier Facélina SECLAB
A Needle in a Haystack: Identifying an Infostealer Attack Through Trillions of Events in a Large-scale Modern SOC
-
François Labrèche Sophos
Measuring AI Ability to Complete Long Cybersecurity Tasks
-
Jeremy Miller OffSec
Teaching AI to Secure Code: How LLMs Deploy Security Frameworks at Scale
-
tanu jain Meta
Adventures in Process Injection (How I Accidentally Built a Debugger - Again!)
-
Ron Bowes GreyNoise Intelligence
Practical AWS Antiforensics
-
Santiago Abastante Solidariy Labs
Closing Ceremony
The end of the 2026 conference!